Ransomware is universal and one of the greatest threats in cybersecurity currently. Extensive research by Sophos has uncovered a trove of new information on the notorious SamSam ransomware that has affected far more victims than previously thought and raised vastly more in ransom demands – almost US$6 million.
Most ransomware is spread in large, noisy and untargeted spam campaigns sent to thousands, or even hundreds of thousands, of people. They use simple techniques to infect victims and aim to raise money through large numbers of relatively small ransoms of perhaps a few hundred dollars each.
What sets SamSam apart from most other ransomware is that it is used in targeted attacks by a skilled team or individual, who breaks into a victim’s network, surveils it and then runs the malware manually. The attacks are tailored to cause maximum damage and ransom demands are measured in the tens of thousands of dollars. The attack method is surprisingly manual and more cat burglar than smash-and-grab.
As a result, the attacker can employ countermeasures (if needed) and is surprisingly adept at evading many security tools. If the process of encrypting data is interrupted, then the malware comprehensively deletes all trace of itself immediately, to hinder investigation.
SamSam is a particularly thorough encryption tool, rendering not only work data files unusable but any program that isn’t essential to the operation of a Windows computer, most of which are not routinely backed up. Recovery may require reimaging and/or reinstalling software as well as restoring backups. The attacker is very good at covering their tracks and appears to be growing increasingly paranoid (or experienced) as time passes, gradually adding more security features into his tools and websites.
Key findings
The basics
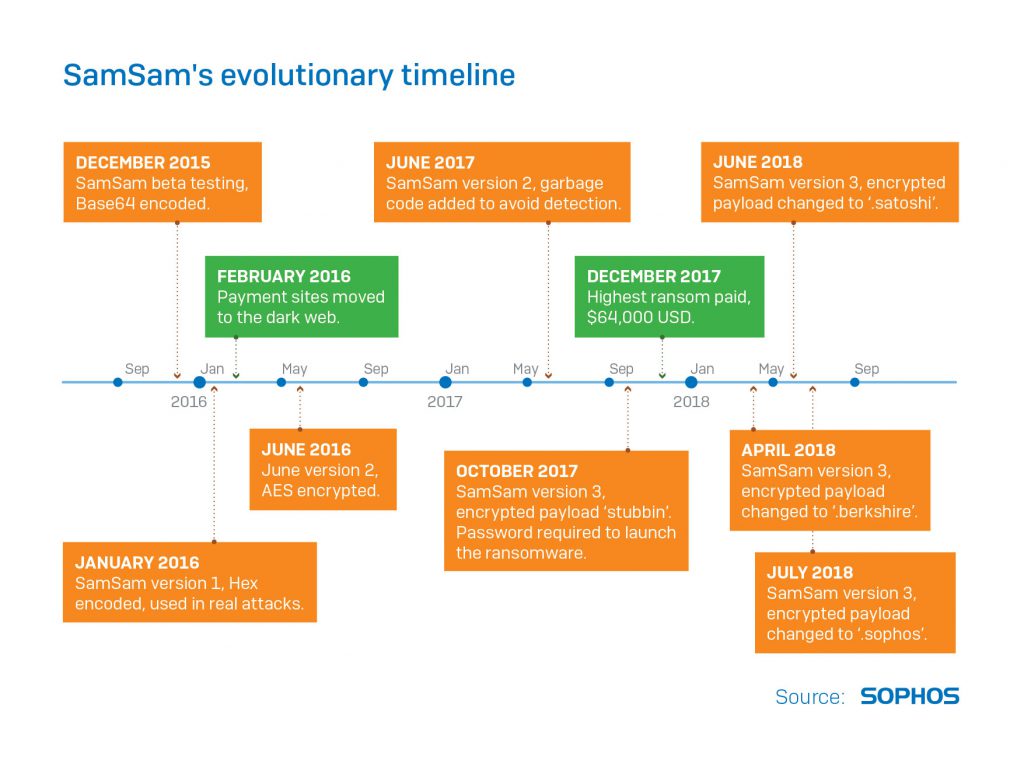
- The SamSam ransomware first appeared in the wild in December 2015
- Some victims reported a widespread ransomware event that significantly impacted operations of some large organisations, including hospitals, schools and cities
- The attack details took some time to obtain because the attacker(s) responsible took great care to obfuscate their methods and delete any evidence that could be revealing
- Many victims found that they could not recover sufficiently or quickly enough to ensure business continuity on their own and reluctantly paid the ransom
The statistics
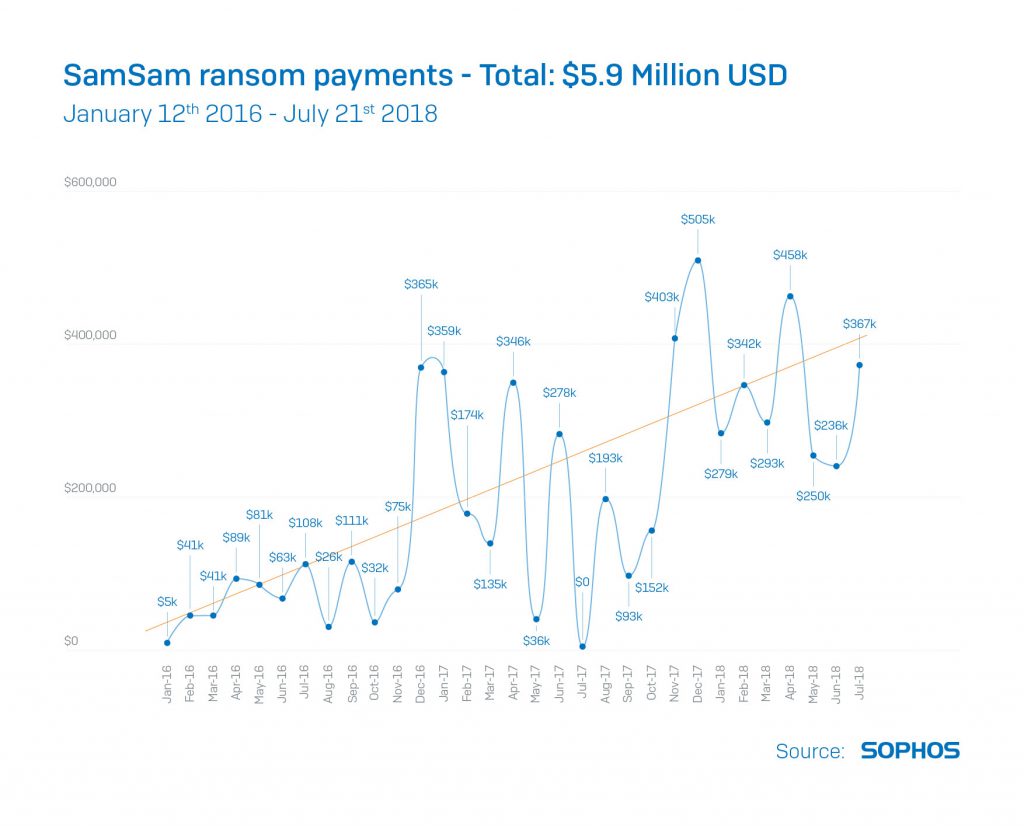
- By tracking Bitcoin addresses supplied on ransom notes and sample files and by working with the firm Neutrino, Sophos has calculated that SamSam has earned its creator(s) more than US$5.9 million since late 2015
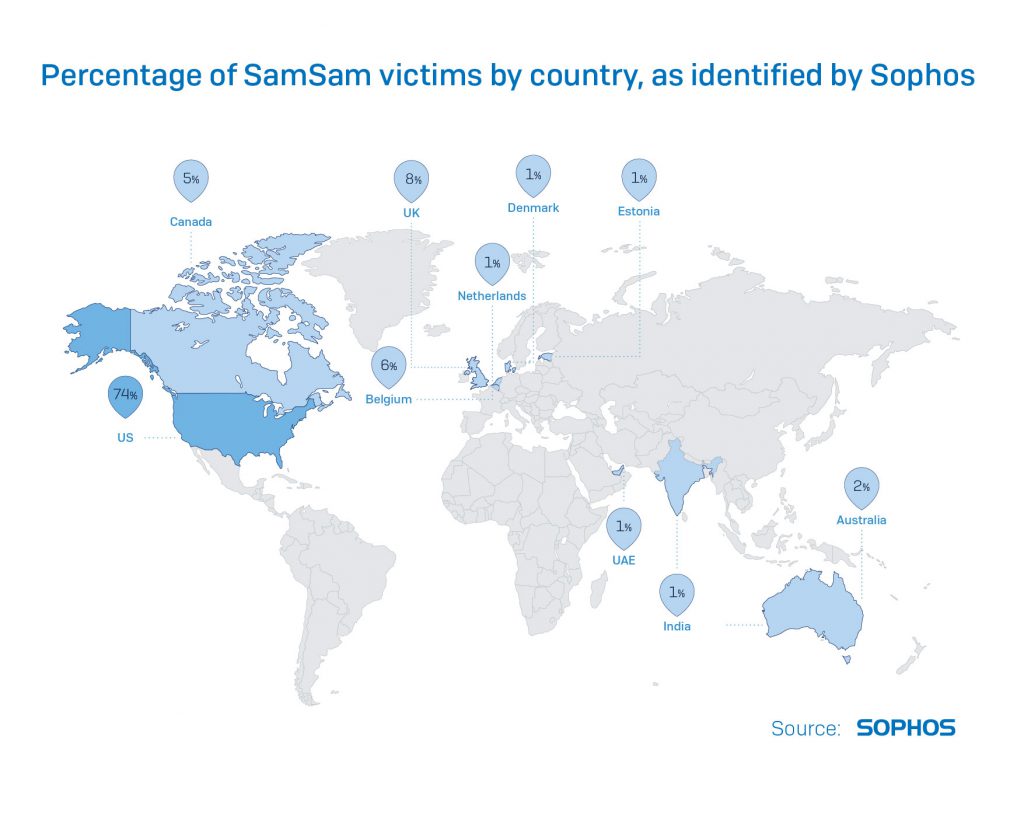
- Sophos has determined that 74% of the known victims are based in the United States. Other regions known to have suffered attacks include Canada, the UK and the Middle East
- The SamSam attacker has received ransom payments as high as US$64,000, based on analysis of ransom payments to the Bitcoin wallets tracked
- Unlike most other ransomware, SamSam encrypts not only document files, images and other personal or work data but also configuration and data files required to run applications (e.g., Microsoft Office). Victims whose backup strategy only protects the user’s documents and files won’t be able to recover a machine without reimaging it first
- Every subsequent attack shows a progression in sophistication and an increasing awareness of how to evade operational security
- The cost victims are charged in ransom has increased dramatically and the tempo of attacks shows no sign of slowdown
The balance sheet
- Sophos estimates that the SamSam attacker earned an average of a hair under US$300,000 per month in 2018. In order to accurately estimate costs, due to wildly fluctuating exchange rates, Sophos calculated the value of a given quantity of Bitcoin as its worth on the day it was acquired by the SamSam attacker, if the SamSam attacker were immediately to cash it out
- From tracking Bitcoin payments made to known wallet addresses owned by the attacker, Sophos has calculated the SamSam take as exceeding US$5.9 million
- The largest single ransom received by the SamSam attacker was valued at US$64,478 (at the time of payment)
- Payment is made by victims in Bitcoin via a custom ‘payment site’ on the dark web that is at a unique address for each victim organisation
- The payment site lets the SamSam attacker interact directly with victims, who use a message board-like interface to communicate
- The ransom amount varies widely by the organisation but has steadily increased over the time the ransomware has been in active use
- After full payment has been received, the SamSam attacker moves the cryptocurrency into a system of tumblers and mixers which attempt to launder the source of the Bitcoin through myriad micro transactions
Recommended security practices
- There is no silver bullet to security; an active and layered security model is the best practice
- If you study the methodology, there are several points at which basic security measures can stop the SamSam attacker
- Sophos recommends implementing these top four security practices right now:
- Restricted access to port 3389 (RDP) by only allowing staff who use a VPN to be able to remotely access any systems. Utilise multi-factor authentication for VPN access
- Complete, regular vulnerability scans and penetration tests across the network; if you haven’t followed through on recent pen-testing reports, do it now
- Multi-factor authentication for sensitive internal systems, even for employees on the LAN or VPN
- Create back-ups that are offline and offsite and develop a disaster recovery plan that covers the restoration of data and whole systems
Additional best security practices Sophos recommends are:
- Layered security that blocks attackers from all points of entry and from gaining access once inside a network
- Rigorous and diligent patching
- Server-specific security with Lockdown capabilities and anti-exploit protection, especially for unpatched systems
- Security that synchronises and shares intelligence to activate lockdowns
- Endpoint and server security with credential theft protection
- Hard to crack and unique IT admin passwords with multi-factor authentication
- Improve password policies: Encourage employees to use secure password managers, longer passphrases and the non-reuse of passwords for multiple accounts – how to pick a proper password.
- Periodic assessments, using third party tools like Censys or Shodan, to identify publicly-accessible services and ports across your public-facing IP address space, then close them
- Improved account access controls: Enact sensible policies to secure idle accounts; automatically lock accounts and alert IT staff after a number of failed login attempts
- Regular phishing tests and staff education about the perils of phishing